Off-road autonomy is no longer “science project” territory. Autonomous hauling is operating at industrial scale in mining: Caterpillar reports trucks with MineStar Command for hauling have moved over 5 billion tonnes autonomously, and Komatsu reports 700+ commercial FrontRunner autonomous haulage deployments as of February 2024. (Caterpillar, 2024; Komatsu, 2024). Yet outside highly controlled domains, many programs still stall between pilot and production. This is primarily an execution problem: operational design, safety assurance, and lifecycle governance are usually harder than the autonomy stack itself.
This whitepaper-style article breaks down the highest-impact off-road autonomy deployment challenges across construction, mining, agriculture, and industrial logistics, using field-realistic constraints and mitigation patterns. The core findings are:
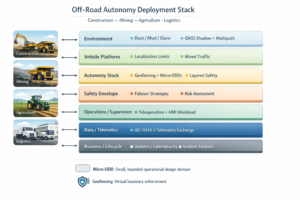
Production scaling requires micro-ODDs/ODEs, not “big bang autonomy.” Treat each route, weather regime, and interaction pattern as a bounded Operational Design Domain (ODD) / Operational Design Environment (ODE) that can be validated and expanded deliberately.
Functional safety must be engineered as a system property with evidence. ISO 17757 sets safety requirements for autonomous and semi-autonomous machine systems in earth-moving and mining contexts; ISO 19014-1 provides a methodology for performance requirements of safety-related control functions and is flagged “to be revised,” reflecting a still-evolving landscape. (ISO, 2019; ISO, 2018). For industrial logistics AMRs/AGVs, ISO 3691-4:2023 defines safety requirements and verification means for driverless industrial trucks and their systems. (ISO, 2023).
GNSS loss is normal in off-road. GPS accuracy is commonly degraded by signal blockage (terrain/structures/trees) and multipath reflections; interference/jamming is less common but high consequence. (GPS.gov, n.d.; FAA, n.d.). Robust deployments depend on multi-sensor fusion (RTK-GNSS + inertial + wheel odometry + LiDAR/radar/cameras, often SLAM-assisted) and clearly defined degraded modes.
Mixed-fleet interoperability is foundational. ISO/TS 15143-3:2020 specifies how machine status data is exposed from telematics provider servers to customer applications; AEMP frames ISO 15143-3 as the telematics standard for mixed-fleet data exchange. (ISO, 2020; AEMP, n.d.). Standardizing data exchange does not solve autonomy by itself, but it drives practical fleet supervision, ROI accounting, and accountability.
Lifecycle operations—updates, cybersecurity, logging, and incident investigation—must be planned as part of certification and customer acceptance. The EU Machinery Regulation (EU) 2023/1230 applies from January 20, 2027, raising the bar for manufacturers and integrators shipping software-intensive machinery. (Pilz, n.d.; TÜV Rheinland, n.d.).
Off-road autonomy deployment challenges when scaling beyond pilots
The most common failure pattern is the “pilot trap”: a prototype shows strong performance under curated conditions, then collapses when exceptions scale faster than support teams.
The scaling hinge is the ODD/ODE boundary, not the autonomy demo
A pilot typically runs inside a soft, undocumented ODD: a known route, a stable site layout, familiar co-traffic, and a handful of trained operators. Production introduces variation: shift changes, contractor vehicles, weather, GNSS shadows, temporary berms, and maintenance downtime. When the ODD boundary is implicit, the first “out-of-ODD” event becomes a safety incident or an availability crisis.
Mining succeeds more often because the environment is engineered for autonomy: geofenced haul roads, disciplined right-of-way rules, and centralized traffic oversight. Rio Tinto describes operating more than 130 autonomous trucks under a supervisory system and central controller using predefined GPS courses to navigate haul roads and intersections—an example of scaling with system-level coordination rather than vehicle-only intelligence. (Rio Tinto, n.d.).
Construction is typically the opposite: the site is dynamic and multi-employer, with frequent reconfiguration. Agriculture adds seasonal variability and boundary conditions (headlands, obstacles, and mixed operations near people and animals). Industrial logistics is structured, but it is “exception rich” (unpredictable pedestrian flows, dock congestion, and frequent path obstructions).
Practical scaling pattern: micro-ODDs + operational hardening gates
A scalable approach is to define micro-ODDs (sometimes called “bounded ODD increments”): one route segment, one maneuver set, one shift pattern, one weather condition. Each micro-ODD gets:
A hazard/risk assessment aligned to safety functions (speed limits, separation monitoring, safe stop, controlled restart).
A verification package (simulation scenarios + replay logs + field acceptance tests).
A monitoring package (telemetry, safety events, near-misses, operator interventions).
This is slow by design—and faster in the long run. It converts scaling from “hope” into a managed expansion program.
Off-road autonomy deployment challenges in functional safety and the safety case
A mature autonomy program is mostly a safety engineering program with software, sensors, and operations attached.
Standards help, but they don’t replace the safety case
For earth-moving and mining, ISO 17757:2019 provides safety requirements for autonomous and semi-autonomous machines and their machine systems used in earth-moving and mining operations. (ISO, 2019). For functional safety performance requirements in earth-moving machinery control systems, ISO 19014-1:2018 defines a methodology to determine safety-related control functions and performance requirements, and ISO lists it as “to be revised,” which is an important signal to program managers: methods and expectations evolve, so traceability and evidence must be maintained over time. (ISO, 2018).
For industrial logistics AGVs/AMRs (“driverless industrial trucks”), ISO 3691-4:2023 specifies safety requirements and the means for their verification. (ISO, 2023). These are not just paperwork artifacts; they define the vocabulary that customers, auditors, and insurers increasingly expect.
Teleoperation and remote control also matter because many “autonomy” deployments rely on remote intervention. ISO 15817:2012 specifies essential safety requirements for remote operator control systems used on earth-moving machinery. (ISO, 2012). Even though ISO 15817 is not an autonomy standard, teleoperation is often the recovery pathway when autonomy fails—so its safety envelope must be engineered into the system concept.
What an evidence-driven safety case looks like in off-road autonomy
A defensible safety case typically includes:
Operational concept and ODD/ODE definition: where autonomy is allowed, including geofencing and speed/behavior constraints.
Hazard analysis tied to site operations: interactions with people, light vehicles, heavy machines, and maintenance activities.
Layered safety functions: independent speed limits, separation monitoring, safe stop, and controlled restart. Layering matters because perception is probabilistic but safety enforcement should be deterministic.
Verification and validation artifacts: scenario libraries (including edge cases), regression test results, field acceptance tests, and operational monitoring results.
Change control for software updates: every update can alter safety behavior; without structured regression testing, confidence collapses.
The main operational failure mode is not “the system is unsafe” but “the system is safe only when babysat”—which is not scalable.
Off-road autonomy deployment challenges in GNSS-denied and degraded environments
If your autonomy strategy assumes “clean RTK everywhere,” it will break. GNSS is a component, not an entitlement.
GNSS degradation is a baseline condition, not a corner case
GPS.gov lists common degraders of positioning accuracy including satellite signal blockage (buildings, bridges, trees), indoor/underground operation, and multipath reflections; it also mentions rarer degraders such as radio interference or jamming. (GPS.gov, n.d.). The FAA’s GNSS interference resource guide defines GNSS interference as interruptions to the GNSS signal-in-space and provides context on GNSS versus GPS. (FAA, n.d.).
In off-road settings, the dominant contributors are practical: pit walls, dense foliage, steel structures, gantry cranes, and moving equipment all create GNSS shadows and multipath.
Multi-sensor fusion is the deployment enabler
Production-grade off-highway autonomous vehicles typically use multi-sensor fusion:
RTK GNSS when available (high absolute accuracy under good sky view).
IMU + wheel odometry for short-term stability and deadreckoning.
LiDAR/radar/camera-based localization against mapped features, often SLAM-assisted (LiDAR SLAM in structured corridors, visual/semantic SLAM where appropriate).
Map management and confidence gating: the system must know when it does not know.
The key is not to “never lose GNSS,” but to define what the machine should do when localization confidence drops: slow down, tighten geofence margins, request remote confirmation, or safe-stop depending on hazard exposure.
Agriculture illustrates the “GNSS is not enough” story well. John Deere’s 2022 autonomous tractor announcement combined an 8R tractor with a GPS guidance system and automated operation intent for production contexts, highlighting mainstream OEM direction: GNSS-guided autonomy with additional sensing and operational constraints. (John Deere, 2022).
Off-road autonomy deployment challenges in mixed fleets, supervision, and lifecycle operations
Most real customers run mixed fleets for decades. Autonomy must fit that reality.
Mixed-fleet interoperability is a prerequisite for scalable operations
ISO/TS 15143-3:2020 describes communication records for requesting telematics data from provider servers and receiving machine performance/management status data—applicable to earth-moving machinery and mobile road construction machinery with location and time instrumentation. (ISO, 2020). AEMP explicitly points to ISO 15143-3 as the telematics standard enabling mobile machinery status data exchange to third-party applications. (AEMP, n.d.).
This matters for autonomy because you cannot manage what you cannot measure. Without standardized telematics:
Dispatch cannot see which machines are ready, stuck, degraded, or in manual mode.
Analytics cannot quantify autonomous vs. manual productivity and downtime.
Incident investigations lack consistent time-aligned machine state.
Even if autonomy control is proprietary, telematics and state reporting should be standardized.
Supervision, HMI, and teleoperation are where scaling breaks
Off-road autonomy shifts labor from “operator in cab” to “supervisor + exception handler.” Supervisor attention becomes the scarce resource. If alerts are noisy, recovery workflows are unclear, or teleoperation interfaces are clumsy, the system “scales” into a bottleneck.
Mining vendors emphasize platform-level control and traffic coordination. For underground loading/hauling operations, Sandvik positions AutoMine Core as a comprehensive automation platform that combines connectivity, data collection/analysis, automated equipment options, and lifecycle support solutions. (Sandvik, n.d.). For surface mining, Epiroc describes Mobius Traffic Management System as a command-and-control system supporting teleoperation and semi/full autonomous modes across applications from drill-and-blast through autonomous haulage systems, and notes continual development through accessible system updates. (Epiroc, n.d.). These descriptions point to an important principle: autonomy is a site operating system, not a vehicle feature.
Lifecycle management, software updates, and cybersecurity are now deployment blockers
Software-defined machines require update pipelines, regression testing, and cybersecurity controls. The EU Machinery Regulation (EU) 2023/1230 replaces the Machinery Directive framework and applies from January 20, 2027, creating a concrete timeline for safety expectations around software-intensive machinery. (Pilz, n.d.; TÜV Rheinland, n.d.).
Digital twins are increasingly used to manage lifecycle risk. NIST describes digital twins as helping monitor status, detect anomalies, predict behaviors, and optimize systems, with applications such as virtual commissioning—a direct fit for validating changes before field rollout. (NIST, n.d.). NISTIR 8356 (draft) specifically discusses cybersecurity challenges presented by digital twin architectures—relevant when twins are connected to operational systems and used in decision loops. (NIST, ~2021).
Mitigation patterns and verification practices
The goal is not “perfect autonomy.” The goal is an autonomy system that is safe, diagnosable, maintainable, and commercially rational.
Key mitigation patterns that repeatedly work across sectors:
Micro-ODD expansion with clear gates: define ODD/ODE at route and maneuver granularity; only expand after passing scenario regression + field acceptance tests and meeting intervention-rate targets.
Layered safety with deterministic enforcement: separate “probabilistic perception” from “deterministic safety envelope” (speed limits, geofencing, independent stop channels, safe-state definitions).
Multi-sensor fusion with explicit confidence and degraded modes: RTK when possible; SLAM/feature localization plus inertial/odometry; operational behaviors tied to confidence, not wishful thinking. Use V2X selectively where infrastructure can enforce right-of-way or provide presence detection, but do not rely on V2X as the sole safety layer.
Digital twin + log replay as the regression backbone: use operational logs to reproduce incidents, generate “scenario shards,” and run repeatable regression before software updates. NIST’s framing of digital twins and virtual commissioning is directly aligned with this pattern. (NIST, n.d.).
Telemetry standardization and state machines: adopt ISO/TS 15143-3 for machine status exposure and define explicit operational states: Autonomous, Assisted, Remote, Manual, Degraded, Safe-Stop, Maintenance. (ISO, 2020).
Incident investigation readiness as design input: instrument time-synchronized “decision traces” (sensor health, localization confidence, planner output, safety controller decisions, remote interventions). Without this, every incident becomes political rather than analytical.
Sector vignettes: what deployment friction looks like in construction, mining, agriculture, and industrial logistics
Construction vignette (autonomous construction equipment): A mid-size contractor pilots an autonomous haul cycle inside a fenced corridor. The first month looks successful; the second month fails as subcontractors introduce new light vehicles and the haul road shifts weekly. The intervention rate spikes because the system was never validated beyond the initial micro-ODD. Mitigation: micro-ODD gating for each corridor change, geofence enforcement, and a field acceptance test checklist integrated into weekly site planning.
Mining vignette (autonomous mining operations): A surface mine adds 15 autonomous haul trucks to an existing fleet. The vehicles perform well, but productivity drops because the traffic management rules and “right of way” behaviors are inconsistently applied at a key intersection. Mitigation: intersection-specific rules, V2X-assisted priority signaling (where reliable), and a supervisory control layer aligned with the way mature operators describe autonomy operations (e.g., supervisory system + centralized control). (Rio Tinto, n.d.).
Agriculture vignette (autonomous agricultural machinery): A farm deploys autonomy for tillage. GNSS works in open fields but degrades near tree lines and in low-angle sun conditions; confidence drops and the machine safe-stops frequently, hurting utilization. Mitigation: sensor fusion with SLAM-assisted localization at boundaries, operational rules for headlands, and explicit “boundary micro-ODDs.” Fraunhofer IKS frames “autonomous agricultural machinery & robotics” as a major smart farming focus area, reflecting the applied-research push toward robust autonomy beyond ideal GNSS assumptions. (Fraunhofer IKS, n.d.).
Industrial logistics vignette (yards, plants, ports, intralogistics): An AMR/AGV program meets safety requirements but struggles with “social navigation” in mixed pedestrian zones; frequent stops cause congestion near dock doors. Mitigation: redesign pedestrian/vehicle separation, enforce speed zoning and right-of-way rules, and treat ISO 3691-4 compliance as the baseline while engineering site workflows to reduce exceptions. (ISO, 2023).
Trends and milestones shaping deployments through 2030
The next decade will reward organizations that build deployment infrastructure: evidence pipelines, update governance, and operational design patterns—not just better neural networks.
Digital twins become the default V&V and operations toolchain
NIST emphasizes digital twins for monitoring, anomaly detection, prediction, optimization, and virtual commissioning. (NIST, n.d.). In construction, Fraunhofer’s building-physics perspective frames BIM-driven digital twins as prerequisites for Construction 4.0 and lifecycle-consistent data management—conceptually aligned with “site twins” used to validate routing, geofencing, and work planning for autonomous machines. (Fraunhofer IBP, n.d.). Expect to see “virtual commissioning” methods move from manufacturing into mines, quarries, and large construction projects where repeating field commissioning is expensive.
Edge-first architectures and connectivity-aware autonomy
Remote sites cannot depend on cloud connectivity for safety decisions. This will push more autonomy stacks toward edge-first compute: local perception, local safety controllers, local map hosting, and local incident logging, with cloud used for analysis and fleet learning rather than real-time control. (This trend aligns with the operational realities highlighted by large OEM efforts in autonomy and the increasing use of digital twins for commissioning and change control.) (John Deere, 2022; NIST, n.d.).
Autonomy-as-a-service and outcome-based commercial models
As autonomy matures, customers will buy outcomes (availability, cost per tonne, cost per moved cubic meter) rather than “autonomy features.” Vendor models will shift toward autonomy-as-a-service (RaaS-like) and performance-based agreements—especially where the vendor also owns the update pipeline and monitoring stack. Epiroc’s description of continual development through accessible system updates in a command-and-control autonomy platform points toward this lifecycle-oriented model. (Epiroc, n.d.).
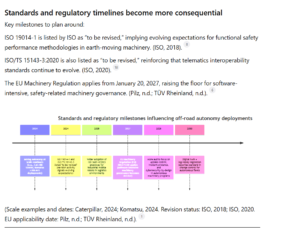
Standards and regulatory timelines become more consequential
Key milestones to plan around:
ISO 19014-1 is listed by ISO as “to be revised,” implying evolving expectations for functional safety performance methodologies in earth-moving machinery. (ISO, 2018).
ISO/TS 15143-3:2020 is also listed as “to be revised,” reinforcing that telematics interoperability standards continue to evolve. (ISO, 2020).
The EU Machinery Regulation applies from January 20, 2027, raising the floor for software-intensive, safety-related machinery governance. (Pilz, n.d.; TÜV Rheinland, n.d.).
(Scale examples and dates: Caterpillar, 2024; Komatsu, 2024. Revision status: ISO, 2018; ISO, 2020. EU applicability date: Pilz, n.d.; TÜV Rheinland, n.d.).
FAQ
What is the biggest root cause behind off-road autonomy deployment challenges?
Not model accuracy in isolation. The dominant root cause is the gap between a demo ODD and production reality: changing environments, mixed traffic, and unmanaged exceptions. Programs that formalize micro-ODDs/ODEs and expand deliberately scale faster with fewer safety incidents.
Which standards matter most for deployment planning?
For earth-moving/mining autonomy programs, ISO 17757 (autonomous/semi-autonomous machine system safety) and ISO 19014-1 (functional safety performance methodology) are core references. (ISO, 2019; ISO, 2018). For industrial logistics AMRs/AGVs, ISO 3691-4:2023 is the key safety-and-verification standard. (ISO, 2023).
How do teams handle GNSS loss without killing productivity?
They treat GNSS degradation as baseline and use multi-sensor fusion (RTK + IMU + odometry + SLAM/localization), plus explicit degraded modes tied to confidence and hazard exposure. GNSS degraders like blockage and multipath are explicitly recognized by GPS.gov as common causes of accuracy loss. (GPS.gov, n.d.).
Why does mixed-fleet interoperability show up in every scaling discussion?
Because operations management, ROI accounting, safety event investigation, and supervision all depend on consistent machine state and telemetry. ISO/TS 15143-3 provides an interface schema for telematics data exchange, and AEMP highlights it as the telematics standard for mixed fleets. (ISO, 2020; AEMP, n.d.).
What changes most between a pilot and production autonomy program?
Governance. Production requires disciplined change control for software updates, formal field acceptance tests, incident logging, and cybersecurity-by-design—